Cybersecurity
Important Steps to Take Before You Recycle a Mobile Phone Number
It’s not unusual to change a mobile number from time to time. For example, when you move, you may want a number that is local to the area you just moved to. Companies also may end up recycling mobile numbers throughout their staff as people come and go.
If you don’t properly detach your mobile phone number from all the accounts it’s used with, you can leave yourself open to identity theft, credit card fraud, and other crimes.
In a 2021 Princeton University study, it was found that 66% of mobile numbers listed as available by major mobile service providers were still connected to accounts on popular sites (Amazon, PayPal, etc.). … Read the rest
Read MoreTop 5 Cybersecurity Mistakes That Leave Your Data at Risk
The global damage of cybercrime has risen to an average of $11 million USD per minute, which is a cost of $190,000 each second.
60% of small and mid-sized companies that have a data breach end up closing their doors within six months because they can’t afford the costs. The costs of falling victim to a cyberattack can include loss of business, downtime/productivity losses, reparation costs for customers that have had data stolen, and more.
You may think that this means investing more in cybersecurity, and it is true that you need to have appropriate IT security safeguards in place (anti-malware, firewall, etc.).… Read the rest
Read MoreMaking Your VoIP Network Bulletproof (Six Tips to Protect Your VoIP from Cyberattacks)
Hardly any phone call system in a business beats VoIP when it comes to efficiency and flexibility. However, it’s not immune to cyberattacks. Discover how you can secure your VoIP ASAP.
What kind of communication system are you using for your business?
I asked because many modern-day businesses have now switched to the Voice Over Internet Protocol (VoIP). This technology allows employees to perform voice calls using only their internet connection.
It’s often a wise choice considering that using VoIP comes with several benefits to a business.… Read the rest
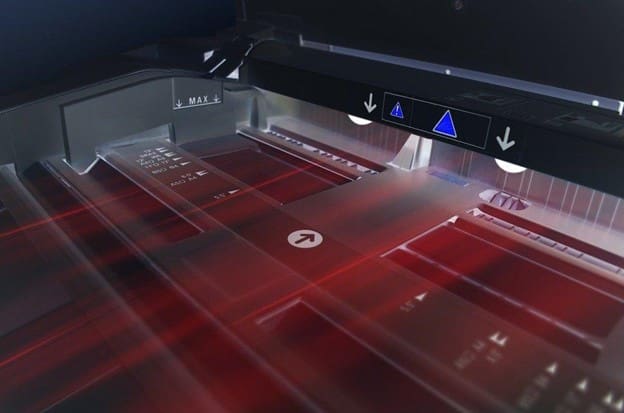
Read MoreWhy Protecting Your Printers from Cybercrime Is a Must (And 8 Tips for Improving Printer Security)
Printing devices are often overlooked when it comes to security. But the reality is, cybercriminals can hack your printer to get confidential information.
Your printer is probably the last piece of computer equipment you thought needed protection from cybercriminals.
But the truth is very different.
Attackers actively try to locate the weakest links in security to gain access to and exploit valuable data. And among the weakest links is the printer.
The thing with printers nowadays is that they have access to your devices, network, and the internet.… Read the rest
Read More